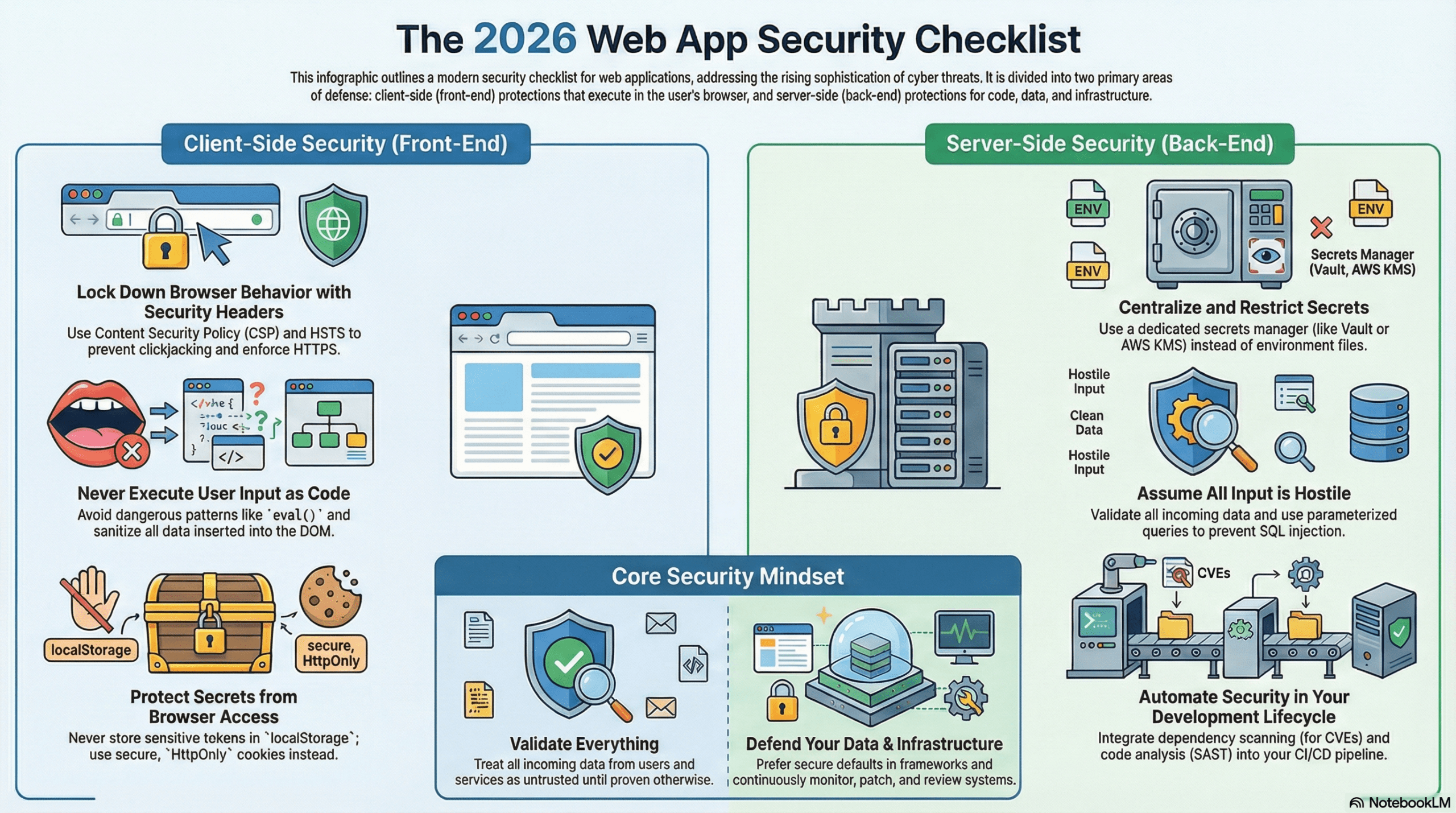
2026 Web App Security Checklist for DevOps & Security Teams. Use this as a living guide to harden your web applications. As AI empowers hackers and attacks become more sophisticated, security must be given utmost priority. Do not rush to publish your app; take time to secure it or prepare to lose it. Here are 12 security best practices to implement in 2026, grouped by CLIENT-SIDE (Front-End) and SERVER-SIDE (Back-End) with special emphasis on defending code execution attacks.

CLIENT-SIDE Front-End Security (Browser Code Execution Defense)
🧾 Security Headers & Browser Protections
✅ Apply a Content Security Policy (CSP) tailored to your app; only allow necessary domains (including any CDNs, e.g., Google Drive, fonts, etc.).
✅ Set `X-Frame-Options` or `frame-ancestors` in CSP to prevent clickjacking.
✅ Enable protections like `X-Content-Type-Options: nosniff` and `Referrer-Policy` with privacy-conscious defaults. ✅ Use `Strict-Transport-Security (HSTS)` to enforce HTTPS.
🧑💻 Client-Side Code Execution Protections
✅ Avoid dangerous patterns like eval(), new Function(), and dynamic script construction from user input; never execute strings as code.
✅ Use frameworks that auto-encode output; avoid manual innerHTML/innerText with untrusted data.
✅ Use CSP nonces/hashes to block inline scripts; minimize third-party scripts and tags.
✅ Sanitize/validate all DOM insertions (APIs, localStorage, third-party data).
✅ Never store long-lived secrets in localStorage/sessionStorage; use HttpOnly cookies.
✅ Implement Subresource Integrity (SRI) for external scripts/CSS.
🖥️SERVER-SIDE Back-End Security (Code & Data Protection)
🔐 1. Configuration & Secrets Management
✅ Use a dedicated secrets manager (cloud KMS, Vault, AWS Secrets Manager, etc.) for API keys, DB passwords, JWT secrets, and never store them directly in `.env` in production.
✅ Restrict who can read secrets (RBAC, IAM policies) and enable audit logs on secret access.
✅ Separate development/staging/production configurations; never reuse production secrets in lower environments.
✅ Enforce strong, random cryptographic keys (sufficient length and entropy) for sessions, JWTs, encryption, and CSRF tokens.
✅ Disable debug/error detail in production; do not log secrets, tokens, or passwords.
🚦 2. Rate Limiting & DoS Protection
✅ Apply rate limiting per IP/user/API key to prevent abuse/DoS (e.g., 100 requests/minute as a sensible default, adjustable per endpoint).
✅ Implement burst + sustained limits (e.g., X per second and Y per minute/hour) and per-endpoint rules for login, password reset, and expensive operations.
✅ Ensure clean‑up of old rate-limit entries to avoid unbounded memory growth.
✅ Use upstream protections: WAF, CDN, or reverse proxy with rate limiting and basic DDoS mitigation.
🧑💻 3. Authentication & Session Security
✅ Use a mature auth framework where possible (password hashing, session handling, CSRF built‑in).
✅ Generate session IDs securely (e.g., `secrets.token_urlsafe(32)` or equivalent high-entropy random IDs).
✅ Mark cookies `Secure`, `HttpOnly`, and `SameSite` (`Lax` or `Strict` according to your use case).
✅ Enforce account lockout/throttling for repeated failed logins (e.g., temporary lock, captcha, or step-up verification).
✅ Store passwords with strong KDFs (e.g., bcrypt/Argon2/scrypt) and never log them.
✅ Validate and rotate JWTs or other tokens; keep expirations short and implement refresh logic carefully.
🔑 4. Authorization & Access Control
✅ Apply role-based access control (RBAC) or attribute-based control for admin and sensitive features.
✅ Enforce server-side checks on every sensitive operation; never rely only on client-side UI restrictions.
✅ Use admin-only endpoints for configuration, user management, and security audit actions.
✅ Check ownership/resource-level permissions (e.g., user can only access own data, not just any valid ID).
🧱 5. Input Validation & Output Encoding
✅ Validate all input (query params, JSON, form data, headers, file uploads) by type, length, format, and allowed values.
✅ Use parameterized queries / ORM bindings for all database operations to prevent SQL injection.
✅ Encode output according to context (HTML, JS, CSS, URL) to prevent XSS rather than manually concatenating untrusted input into templates.
✅ Reject or sanitize dangerous file types and enforce file size limits; scan uploads where appropriate.
🗄️ 6. Database & Storage Security
✅ Use strict SQL modes, strong authentication, and least-privilege DB accounts (separate read/write roles).
✅ Enforce TLS/SSL connections to the database in production.
✅ Avoid exposing DB ports directly to the internet; put them behind private networks/VPCs or VPN.
✅ Ensure logs and backups are stored encrypted, access-controlled, and rotated.
🧠 7. Cache & State Management
✅ Use thread/process-safe mechanisms (locks or equivalent) where needed to protect shared in-memory caches.
✅ Set cache size limits and eviction policies to prevent memory exhaustion.
✅ Define cache expiry to avoid serving stale or sensitive data for too long.
✅ For shared caches (Redis, Memcached), require authentication and network isolation.🌐 9. API & Microservices Security
✅ Use authentication (e.g., OAuth2/JWT/API keys) for internal and external APIs.
✅ Enforce CSRF protection on state-changing endpoints exposed to browsers, with careful exemptions only where truly safe.
✅ Validate input on every API endpoint; never trust upstream services blindly.
✅ Version your APIs and carefully deprecate old versions; avoid exposing debug or testing routes in production.🐛 10. Error Handling, Logging & Monitoring
✅ Implement centralized logging for security events: failed logins, permission denials, suspicious requests, and rate-limit triggers.
✅ Log IPs and user identifiers where allowed by privacy regulations, and protect log integrity and access.
✅ Provide a 429 (Too Many Requests) handler and clear error responses without leaking stack traces or configuration details.
✅ Include a security audit/health endpoint for admins only, summarizing key security status (e.g., debug off, HTTPS on, config checks).
🛡️ 11. Transport & Platform Security
✅ Enforce HTTPS everywhere; redirect HTTP to HTTPS and use modern TLS settings.
✅ Keep OS, runtime, framework, and libraries updated; enable automatic security patches where possible.
✅ Run apps with least privilege (non-root users, minimal capabilities, container isolation).
✅ Harden containers/VMs: minimal base images, firewall rules, and no unnecessary services.
🧪 12. Secure Development Lifecycle
✅ Integrate SAST/DAST tools into CI/CD to catch common vulnerabilities early.
✅ Perform dependency scanning for known CVEs and keep dependencies patched.
✅ Run regular penetration tests and security reviews, especially before major releases.
✅ Document and rehearse an incident response process (detection, containment, remediation, communication).
🧭 Quick Heuristic for Everyday Use: Treat secrets as high-risk assets and keep them in the security manager’s hands. Assume all input is hostile until validated. Prefer secure defaults in frameworks and infrastructure. Monitor, patch, and review security continuously as part of normal DevOps practice. Keep in mind this is not an exhaustive list; be mindful of other security best practices.